Controlled Unclassified Information (CUI) is sensitive data not classified yet and demands vigorous protection. Companies such as government contractors, IT providers, and defense services providers should adhere to rigorous cybersecurity requirements when dealing with CUI.
When you are looking at what type of level of system and network is needed to have CUI, then the simple answer is
“CUI needs a moderate level of system and network security for confidentiality.”
What is CUI (Controlled Unclassified Information)?

CUI is sensitive information that is not classified yet requires protection according to the rules of the government and cybersecurity systems. It helps in ensuring that significant information is managed safely in every company.
CUI aids in standardizing the way sensitive data is stored, processed, and shared to avoid abuse or unauthorized access.
Types of Data CUI Covers
CUI contains many types of sensitive information to be safeguarded:
- Contract data of the government with operational details.
- System documentation, engineering drawings, and technical designs.
- Monetary documents and personally identifiable information (PII)
Such data might not be classified, but the release of such information can be devastating to organizations.
The significance of CUI Security

CUI security is important to ensure that sensitive but non-classified information is not exposed to cyber threats and abuse.
Lack of protection may expose organizations to severe financial, legal, and reputational risks.
Risk of Data Breaches
Without appropriate security of CUI, attackers might exploit vulnerabilities in the systems and access sensitive data. This may result in theft of data, destruction of systems, or even a disruption to the operations.
Legal and Compliance Consequences
There are strict regulations that have to be adhered to by organizations dealing with CUI. The failure to do so may lead to penalties, audits, or even loss of government contracts.
Issues of Reputation and Trust
CUI breach of security may weaken the relationship between the organizations, clients, and government agencies, and later on, the business relationship between the parties.
Which level of system and network is needed in CUI?
Both the system and network environments of CUI need a Moderate Confidentiality Security Level.
This level provides a high level of protection and does not impair system usability and performance effectiveness.
Meaning of Moderate Level of Confidentiality
Moderate confidentiality refers to the system being designed in such a way that it is sensitive to the data it tries to safeguard but does not make its functioning overly complicated or restrictive.
It focuses on:
- Preventing unauthorized access to data.
- Maintaining the stability of systems.
- Lessening the chance of cyber attacks.
- Having controlled access by the users.
This tier is mostly applied in governmental and contractor-based settings.
Basic Framework on CUI Protection

To safeguard CUI data in a proper manner, organizations have to adhere to the set security frameworks.
It is one of the most significant frameworks that is common in systems relating to government.
NIST SP 800-171 Standard
The main guideline in the protection of CUI in non-federal systems is the NIST SP 800-171.
It ensures:
- Data confidentiality protection
- System integrity maintenance
- Authorization of users to access the system.
This framework offers structured guidelines to apply security controls in an effective manner.
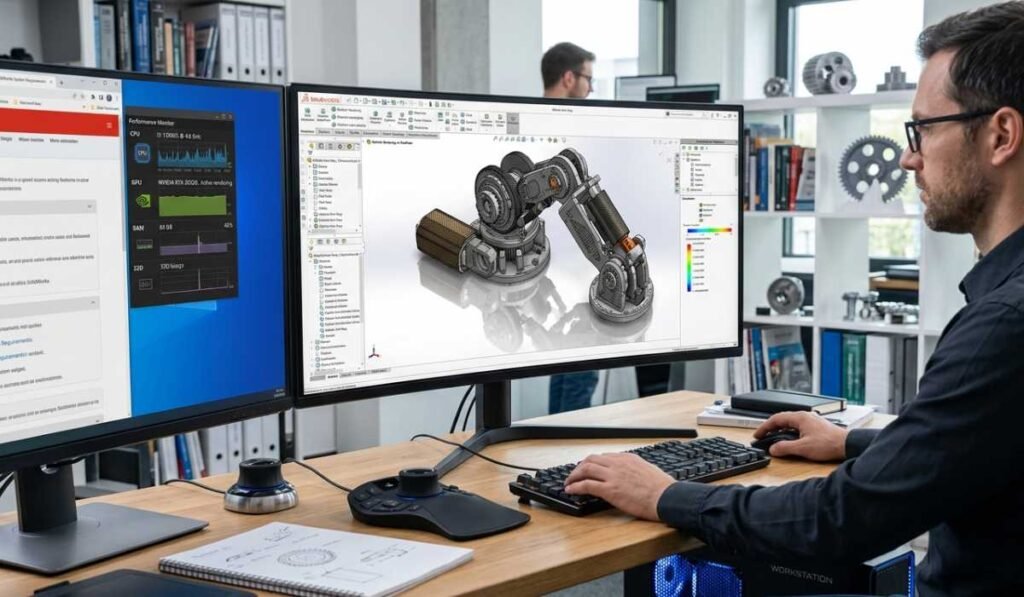
CUI System Requirements
CUI systems should be reliable, up-to-date, and able to ensure robust security measures.
These ought to accommodate performance and cybersecurity needs without compromising on data safety.
Operating System Requirements
CUI environments should be based on modern and supported operating systems in organizations.
These can be Windows, Linux, or MacOS systems that are regularly updated with security updates. There should never be an antique system since it has its loopholes.
Hardware Requirements
Systems must incorporate:
- Minimum RAM of 8GB (16GB suggested)
- A solid-state drive (SSD) can speed up the processing of data.
- Multi-core processors to achieve efficiency.
Stability and Maintenance of Systems
CUI systems need to be continuously revised and maintained to keep them safe against emerging threats and vulnerabilities.
Security Features Required in Systems
System-level security is needed to defend CUI against unauthorized access and cyber threats.
Access Control Mechanisms
Access control is used to make sure that users can access particular data or systems only when they are supposed to, based on their roles.
Authentication Requirements
CUI systems require strong authentication that consists of:
- Strong password policies
- Unique user identification
- Multi-factor authentication (MFA)
Endpoint Protection
The devices that are linked to CUI systems should be safeguarded by antivirus software, firewalls, and real-time surveillance tools.
System Hardening
System hardening enhances security by minimizing vulnerabilities by:
- Removing unused applications
- Disabling unnecessary services
- Sealing unneeded network ports.
- The use of routine security patches.
CUI Network Requirements

Network security is a very important aspect of securing CUI against outside and insider threats.
An effective network lowers the chances of unauthorized access and data leakages.
Firewall Protection
Firewalls provide a security barrier between the trusted and untrusted networks as well as preventing suspicious traffic and unauthorized access.
Network Segmentation
Network segmentation breaks down the network into smaller and secure segments to restrict access and manage data flow.
This helps in:
- Reducing attack spread
- Limiting unauthorized access
- Improving monitoring efficiency
Secure Communication Channels
To ensure data protection during transit, organizations should employ communication protocols that are secure, like HTTPS, VPNs, and an encrypted intranet.
CUI Encryption Requirements

The typical stages of the data lifecycle must be secured with encryption.
Encryption of Data at rest
The data stored should be encrypted to ensure that it cannot be read in the event that someone gains access to it without the necessary authorization.
Encryption during Data Transfers
Information that travels on networks should also be encrypted so as to avoid being intercepted or modified illegally.
Notable Security Controls of CUI
To provide complete security, organizations should establish various levels of security measures.
These controls assist in keeping up with compliance and minimizing cyber risks.
- Access management systems
- Audit recording and surveillance.
- Risk assessment procedures
- Configuration management
- Incident response planning
Audit and Monitoring

Monitoring should be a continuous process so that any threats can be identified in time to keep the systems secure.
Activity Tracking Systems
Accountability and detection of suspicious behavior should be done by logging and reviewing all the activities of the users.
Threat Detection Systems
Security tools assist in the detection of abnormal activities in real time so that prompt action can be taken in case of an attack.
Log Management
Logs should be locked and checked on a regular basis to ensure compliance and forensic analysis.
Incident Response at CUI Systems

To manage cyber threats, organizations need to have an organized incident response strategy.
Detection and Response
The security teams should promptly detect and act on threats to reduce the damage.
Recovery and Restoration
Systems should be restored to normal operations after an incident in a safe manner.
Reporting and Compliance
Any incidents should be recorded and reported as per the regulations.
Cloud Role in CUI Security

Cloud computing is significant in the storage and management of CUI data in a safe manner.
Scalability Benefits
The cloud systems enable organizations to expand or contract resources depending on the demand.
Built-in Security Features
The majority of the cloud platforms have encryption, access control systems, and monitoring tools.
Backup and Recovery Systems
Cloud environments provide backup and rapid recovery facilities in the event of system failure or loss of data.
Common Mistakes in CUI Security
Companies cannot get CUI because of some preventable errors:
- Weak or used passwords.
- Absence of multi-factor authentication.
- Obsolete software and systems.
- Poor network segmentation
- Absence of constant observation.
Best Practices of CUI Compliance

The process of CUI security is a continuous effort and best practice.
Patch Management and regular updates
Systems should be frequently updated to correct vulnerabilities and enhance security.
Employee Training Programs
Threats like phishing and social engineering attacks should be taught to employees.
Security Testing/Audits
Organizations must carry out frequent
- Vulnerability scans
- Penetration testing
- Security audits
Continuous Monitoring
Monitoring of security should be 24/7 in order to detect and react to threats on a real-time basis.
Conclusion
Knowing the level of system and network necessary to have CUI is crucial in organizations that deal with sensitive information that is not categorized as classified.
CUI needs the security level of Confidentiality (Moderate) that will provide a high degree of protection and at the same time will not affect the usability of the system. Through adherence to guidelines such as NIST SP 800-171, installation of appropriate system and network security, and ongoing monitoring, organizations will be in a position to attain complete compliance and secure their data.